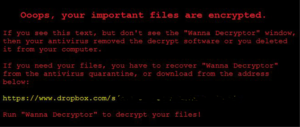
Ransomware attacks unpatched systems
 In recent weeks, there has been several instances that have cost businesses a lot of anguish, efforts to recover data and services. One of the major issues are certain types of attacks that do succeed and have devastating results. How would Cyber Essentials have saved your organisation?
In recent weeks, there has been several instances that have cost businesses a lot of anguish, efforts to recover data and services. One of the major issues are certain types of attacks that do succeed and have devastating results. How would Cyber Essentials have saved your organisation?
In short there are several questions based on specific attacks that have happened previously and what you needed to do to avoid them.
These questions cover whether you have changed the default password on your firewall and router to implementing some mandatory firewall rules.
Which rules should be implemented as extra?
Question 4
Have all commonly attacked and vulnerable services (such as Server Message Block (SMB), NetBIOS tftp, RPC, rlogin, rsh, rexec) been disabled or blocked by default at the boundary firewalls?
These rules should be enabled for both Ingress (inbound) and Egress (outbound). These are ports 135, 139, 445 and 3389. How does this stop anything? A recent leaked set of attack tools from the National Security Agency exploited these protocols. This is a very commonly exploited attack. In a mild form of the attack Windows systems will automatically send your user name, domain name and a hashed version of your password to the attacker. These passwords can be cracked very quickly, but usually there is no need, the attacker can just replay the credentials back to the device for instant access.
Question 31
Are all Operating System security patches applied within 14 days of release?
MS017_010 is a very critical patch that was released on 14 March 2017. It should have been treated as a priority.
Currently there are several ransomware attacks in progress hitting the NHS in England, GP surgeries connected to the network. They are not alone in this, hundreds of smaller businesses have been hit by this. Patching of critical updates are mandatory.
Question 14
Do you have a backup policy in place, and are backups regularly taken to protect against threats such as ransomware?
This is vital if you wish to recover from a ransomware attack. No backups mean that your are not going to recover.
If you have concerns please contact [email protected] for more help and information on getting certified.